[ losm1 @ 07.03.2011. 19:13 ] @
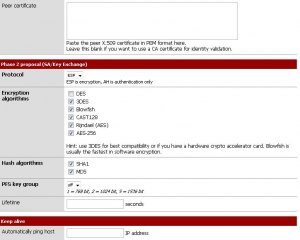
| Pokušavam da konfigurišem jedan cisco access router da funkcioniše kao VPN server. Kao klijent koristim Cisco VPN Client 5.00.07.290. Ispratio sam neka uputstva ali klijent baca grešku 433. Konfiguracija sledi, debug crypto isakmp je u prilogu, gde grešim? ! version 12.4 service timestamps debug datetime msec service timestamps log datetime msec no service password-encryption ! hostname box ! boot-start-marker boot-end-marker ! logging buffered 51200 warnings enable secret 5 xxxxxxxxxx ! aaa new-model ! ! aaa authentication login vpnclient local aaa authorization network localgroups local ! aaa session-id common ! resource policy ! mmi polling-interval 60 no mmi auto-configure no mmi pvc mmi snmp-timeout 180 ip subnet-zero ip cef ! ! no ip domain lookup ! ! voice-card 0 ! ! username vpnuser secret 5 xxxxxxxxxxx ! ! crypto isakmp policy 10 encr aes 256 authentication pre-share group 2 crypto isakmp keepalive 20 10 ! crypto isakmp client configuration group vpn-access key test dns 192.168.1.1 domain ls49.org pool vpn-addr acl acl-vpn include-local-lan max-users 2 max-logins 2 ! ! crypto ipsec transform-set client-transform esp-aes 256 esp-sha-hmac ! crypto dynamic-map dynmap 10 set transform-set client-transform ! ! crypto map map-0 client authentication list vpnclient crypto map map-0 isakmp authorization list localgroups crypto map map-0 client configuration address respond crypto map map-0 1000 ipsec-isakmp dynamic dynmap ! ! interface FastEthernet0/0 ip address 10.0.0.254 255.255.255.0 duplex auto speed auto no cdp enable ! interface FastEthernet0/1 ip address 192.168.1.10 255.255.255.0 duplex auto speed auto crypto map map-0 ! interface Serial0/1/0 no ip address shutdown clock rate 2000000 ! ip local pool vpn-addr 10.0.0.1 10.0.0.15 ip classless ip route 0.0.0.0 0.0.0.0 FastEthernet0/0 ! ! ip http server ip http access-class 23 ip http authentication local ip http secure-server ip http timeout-policy idle 60 life 86400 requests 10000 ! ip access-list extended acl-vpn permit ip 10.0.0.0 0.0.255.255 any ! access-list 23 permit 192.168.0.0 0.0.255.255 access-list 101 permit ip 192.168.0.0 0.0.255.255 any ! ! control-plane ! ! line con 0 line aux 0 line vty 0 4 access-class 23 in transport input telnet ssh line vty 5 15 access-class 23 in transport input telnet ssh ! end |